Become Less Reactive in Your Cyber Strategy
Today, the threat landscape and the constant pressure to manage resources effectively means addressing the risks tied to legacy applications and technologies while maintaining a balance between security and usability is paramount. It’s crucial to align your cyber and data strategies to safeguard critical information assets.
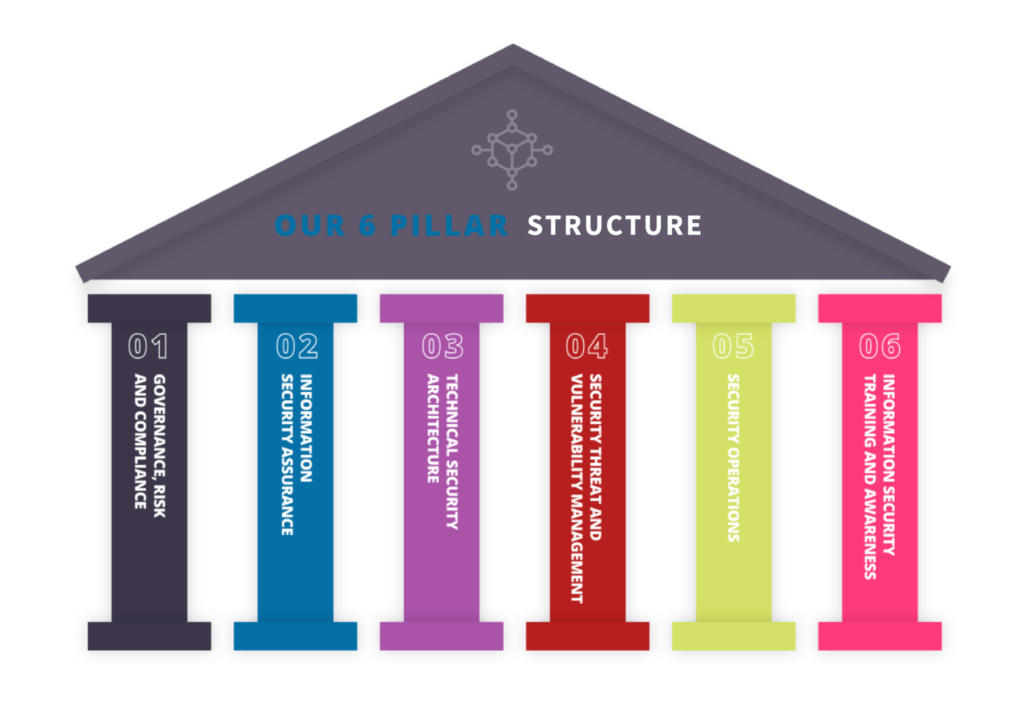
This is where our Security Target Operating Model (STOM) methodology comes in. It’s your blueprint to navigate the ever-evolving Cyber Threat landscape, ensuring your business stays resilient and secure in the face of modern threats.
Undertake a Holistic Review of Your Cyber Posture and Hygiene

Cyber Research Centre:
Staffed by our team of Cyber & Data Centre experts, we actively analyse testing data, industry alerts, vulnerability trends and more to feed into the remediation guidance and cyber security maturity roadmaps we develop for our customers.

Insights
Cutting edge insight and analysis on emerging cyber threats and vulnerabilities that enable us to adapt and better protect our customers IT environments.
Innovation
Influences the development of innovative solutions, strategies and technologies to enhance cyber security and protect critical information infrastructure.

Knowledge
Research uncovered is used as knowledge-sharing between our customers and partners.

Action
Provides actionable insights, recommendations, and tools to mitigate cyber risks and strengthen the resilience of organisations against cyber attacks.

End-to-End Cyber Security Solutions