Become Less Reactive in Your Cyber Security
Many customers expressed their frustration with a sense of reactivity in their cyber strategies, investing in isolated solutions to address individual issues rather than following a comprehensive blueprint that aligns with their broader business objectives.
Frameworks such as the NIST Cyber Security Framework, offer valuable guidance. However, we identified a crucial need for a cyber strategy blueprint that seamlessly integrates with specific and evolving business requirements. We understood this, listened and invested in our cyber practice.
MTI's Security Target Operating Model
MTI’s Security Target Operating Model methodology is your blueprint to navigate the ever-evolving IT landscape, ensuring your business stays resilient and secure in the face of modern threats.
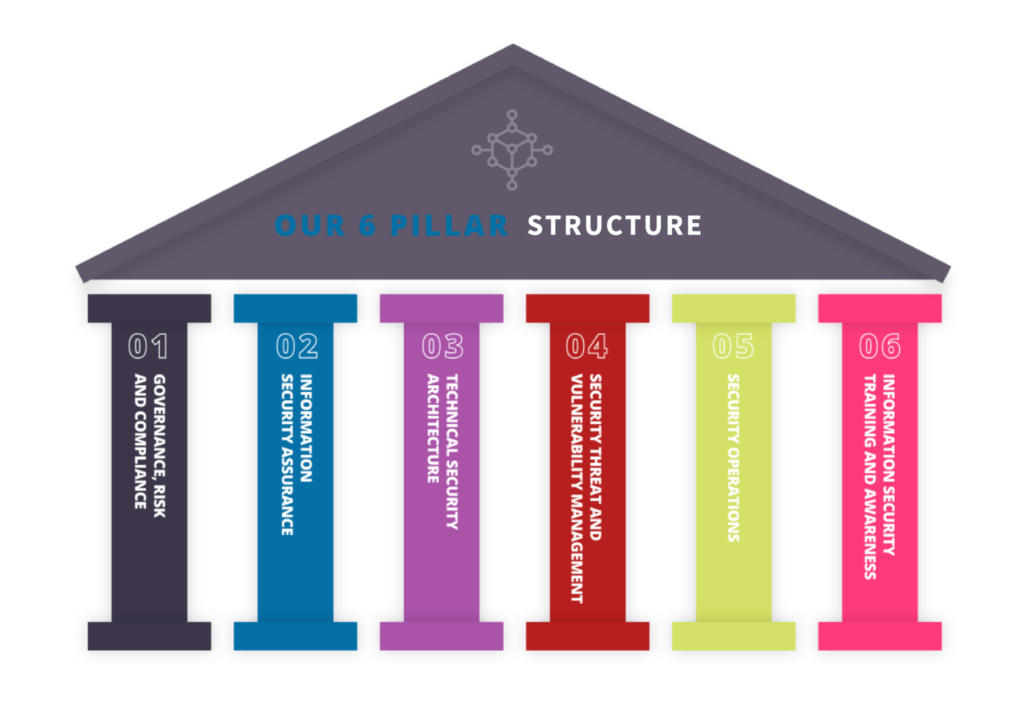
With the Methodology, you can discover any risks relating to data within the organisation. It’s a three stage process, and depending on what is identified within the first discovery phase, this will inform the structure and the contents of the remediation and resilience plan and the focus areas. The contents of which will fit into our 6 pillar structure.
Align Your Strategy to Recognised Frameworks
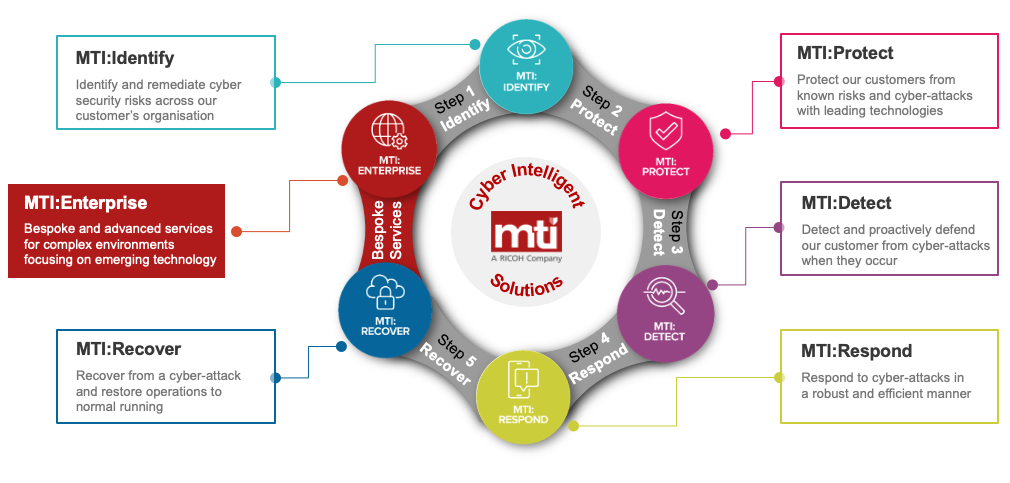
Our cyber security portfolio of solutions and services are aligned to the NIST Cyber Security Framework.
These can be accessed through the 6 pillars in the Security Target Operating Model. The solutions and services positioned will all be aligned to what was identified in the first stage of the Security Target Operating Model and will be unique to your blueprint.
This guides our customers through a recognised cyber security framework with a structured approach for any cyber security requirement.
Best in Class















We have extensive experience in managing diverse threats and attacks. As proud members of esteemed global cyber security organisations like CREST and CHECK, we possess a wealth of knowledge and skills in identifying risks and implementing effective remediation measures.
Our extensive experience and expertise have earned us a reputation as a dependable partner for organisations looking to reinforce their cyber security and mitigate potential risks.
Find a service that's right for you...
Consult & Advise
Technology centric and siloed projects just don’t cut it any more. Explore our Security Target Operating Model Methodology to define your strategy and enhance your cyber resilience.

Assess and Identify
Our Security Assessment services allow organisations to combat areas of vulnerability while providing a plan to mitigate risks. Our in-house security team take a consultative approach to projects to ensure business are comfortable with each stage of the project.

Design and Deployment
We take time to understand your business requirements and current resources or recommend introducing new resources to meet evolving business and organisational needs.

Source and Procure
We collaborate with industry-leading cyber security vendors, consistently assessing our portfolio to guarantee our customers derive optimal value from their solutions

Manage and Enhance
We offer a range of cyber security managed services to provide you with efficient and effective management of your data centre operations. By outsourcing responsibility to us (MTI), you can focus on your core business activities, while we take care of the day-to-day management.
Penetration Testing Services
With MTI, you can rest easy knowing that our extensive experience in conducting penetration testing on both internal and internet-facing infrastructure will provide you with the best possible protection against cyber threats.
- Founding CREST member
- 35+ Years experience with best in class testing team
- All testing requirements covered
- Pen Testing Packages & Managed Services
Why MTI?

Over 3 decades of experience as a trusted IT services and solutions provider

Our priority is to streamline your IT operations, up skill your teams & reduce operational burden
We are a safe pair of hands with highly-accredited teams and long standing relations with our key partners

Our portfolio extends from assessment, design, deployment support and ongoing management
Part of the Ricoh family, our customers can access a global network of specialists


Read the latest customer experience
End-to-end, high-performance infrastructure and managed service delivering secure learning across multiple campuses
Our top-tier partnerships delivering best in class protection for your organisation